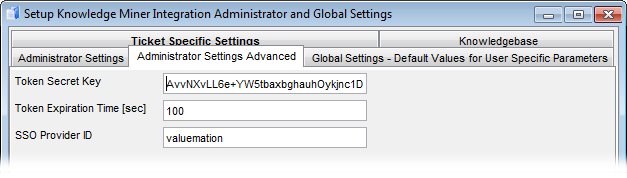
Administrator Settings Advanced
Settings for secure token communication. Three crucial settings are available:
- Token Secret Key
All requests from the user to KnowledgeCenter have to be authorized. In order to eliminate the need for users to log in whenever a request from Valuemation to KnowledgeCenter is sent, Single Sign On token is used.
- The token is based on a token secret key issued by the GateKeeper (a KnowledgeCenter suite auxiliary application dealing with user and their access rights).
- Token secret key is used by Valuemation to generate SSO token (from the secret key, user name, SSO Provider ID and current time).
- This token is used by the GateKeeper to authorize the user's request without the need to log in.
Note that for the authorization to work, user names in the Valuemation database must correspond to user names in GateKeeper.
Value: This information will be provided by your KnowledgeCenter/GateKeeper administrator.
- Token Expiration Time [sec]
Valuemation-created SSO token contains information about the time of its creation. Token expiration time specifies the time period (in seconds) for which the token is considered valid. If Valuemation SSO token is received by the Gatekeeper at a time exceeding the time of SSO token creation plus token expiration time, then it is considered invalid.
The token expiration time parameter has one important role: it can be used to compensate for possible system time difference between the Valuemation and GateKeeper server. The more desynchronized the two servers are, the higher token expiration time must be set for the token exchange to work.
- SSO Provider ID
When the GateKeeper receives an SSO token, it checks that it also contains expected identification of the application sending the SSO token (SSO provider). For Valuemation - KnowledgeCenter communication the expected SSO provider ID is 'valuemation'. This value is taken from GateKeeper internal settings made for the Valuemation - KnowledgeCenter communication and is not supposed to be changed.